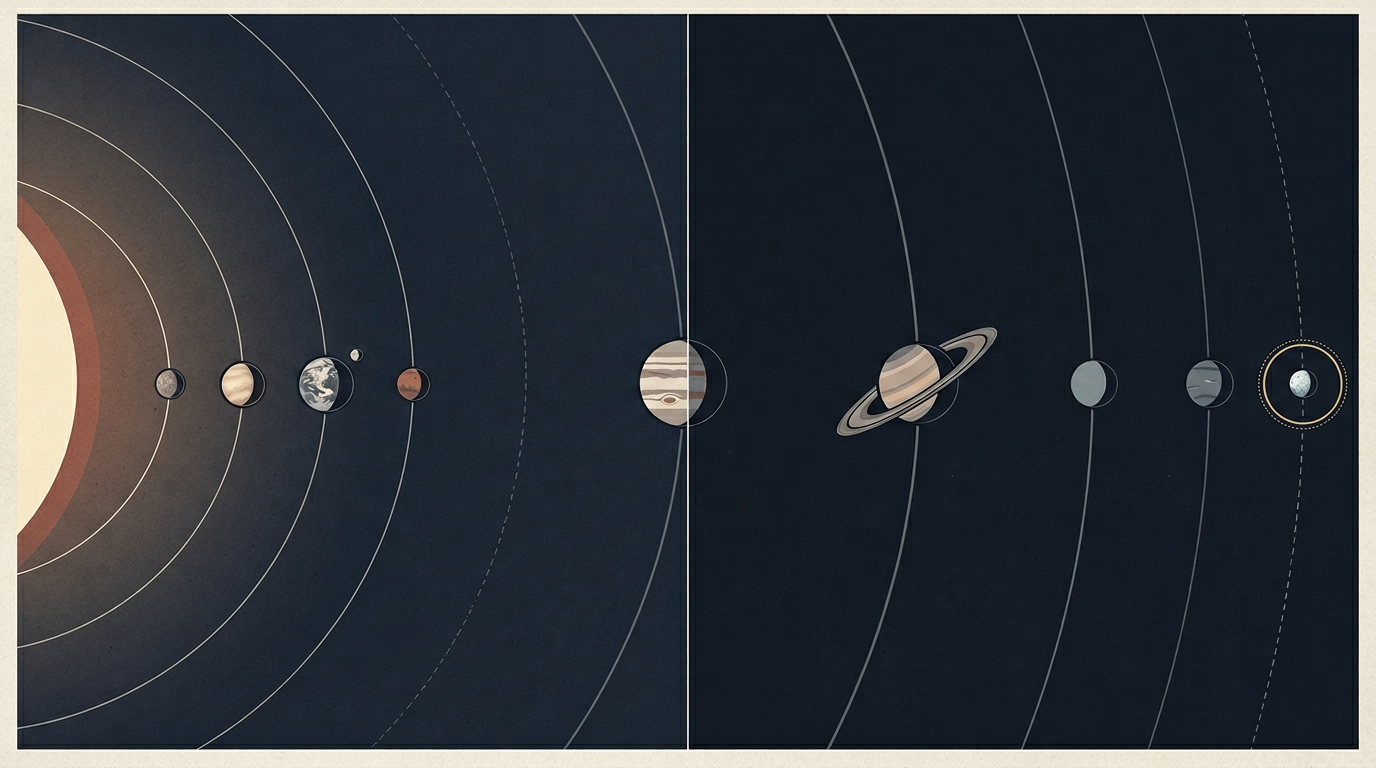
Modern military power is increasingly an exercise in orbital logistics. From the precision of global positioning to the real-time data flows that guide tactical decisions, the ability of the United States to operate on a global scale is fundamentally anchored in space. This dependence has transformed low Earth orbit from a silent vacuum into a critical infrastructure layer — one as vulnerable to bits and bytes as it is to physical projectiles.
The strategic shift is becoming visible in policy. The President's Cyber Strategy for America and the Joint Staff's recent operational frameworks now treat space not as a separate domain, but as a vital component of "non-kinetic" effects. By grouping space with cyber, electronic warfare, and information operations, military planners are acknowledging that the next conflict may not be won by destroying a satellite, but by hijacking its signal or blinding its sensors through digital means.
From Kinetic Threats to Digital Vulnerabilities
For decades, the dominant concern in space security was kinetic: anti-satellite missiles, orbital debris, and the physical destruction of hardware that costs billions to build and years to replace. China's 2007 anti-satellite missile test, which destroyed one of its own weather satellites and generated thousands of trackable debris fragments, served as a watershed moment in that paradigm. Russia has conducted similar demonstrations. But the threat landscape has since evolved in ways that make kinetic attacks look almost crude by comparison.
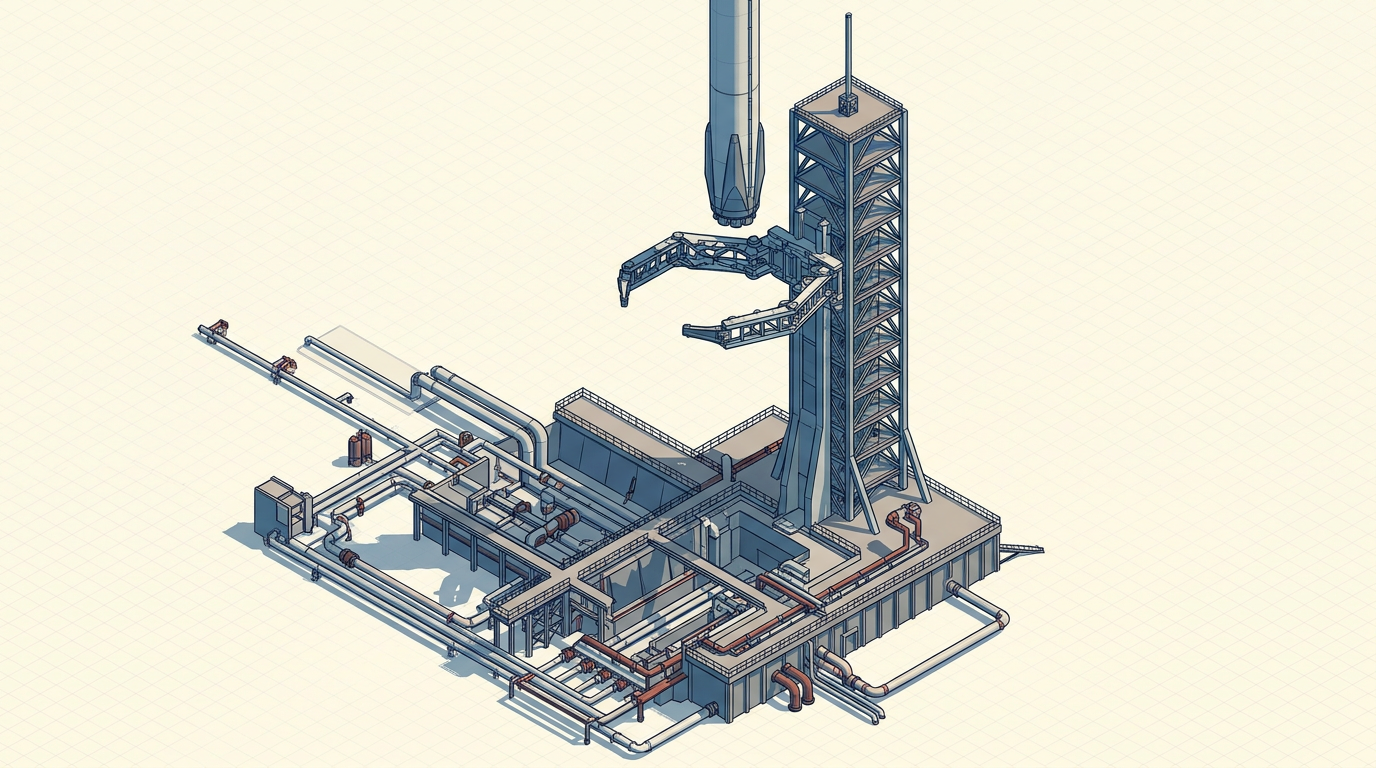
A cyberattack on a satellite's ground control segment or its communication links can achieve strategic disruption without producing a single piece of debris — and without triggering the kind of international condemnation that a kinetic strike would invite. Jamming and spoofing of GPS signals have already been documented in conflict zones, offering a preview of what a more sophisticated campaign might look like. The attack surface is broad: ground stations, uplink and downlink frequencies, onboard software, and the supply chains that produce satellite components all present potential entry points.
The challenge is compounded by the growing entanglement of military and commercial space infrastructure. The U.S. military relies heavily on commercial satellite constellations for communications, imagery, and data relay. This dual-use architecture creates efficiencies but also multiplies the number of nodes an adversary could target. Securing a network that spans government-owned assets and privately operated constellations requires coordination frameworks that traditional defense procurement was not designed to handle.
Integration as Doctrine
Through the United States Space Force, established in 2019 as the first new branch of the U.S. armed forces in over seven decades, the focus is moving toward resilience and integration. The decision to fold space operations into the broader architecture of cyber and electronic warfare reflects a doctrinal recognition: that orbital assets are not standalone platforms but nodes in a larger information network. Defending them requires the same disciplines — threat intelligence, penetration testing, encryption, anomaly detection — that apply to terrestrial cyber infrastructure, adapted for the unique constraints of space-based systems where patching software on a satellite in orbit is not a trivial exercise.
This integration also carries organizational implications. Historically, space operations, signals intelligence, and cyber defense sat in separate bureaucratic silos. Treating them as components of a unified non-kinetic domain demands new command relationships, shared threat databases, and joint training pipelines. Whether the institutional culture of the Department of Defense can adapt at the speed the threat environment demands remains an open question.
The broader geopolitical dimension adds further complexity. International norms governing cyber operations in space remain largely unwritten. The Outer Space Treaty of 1967 prohibits weapons of mass destruction in orbit but says nothing about malware. Establishing rules of engagement for cyber conflicts that unfold across orbital infrastructure would require multilateral agreements among precisely the nations most likely to be adversaries in such a contest.
As the boundaries between hardware and software continue to blur, the defense of the final frontier is less about physical armor and more about robust encryption and network security. The highest ground in the modern theater of war is no longer just a physical location — it is the digital architecture that keeps it connected. Whether the institutions charged with defending that architecture can evolve as fast as the threats targeting it is the tension that will define space security for the coming era.
With reporting from SpaceNews.
Source · SpaceNews