For decades, the video game industry's primary threat to secrecy was the disgruntled employee or the loose-lipped tester. Today, that landscape has shifted toward industrial-scale espionage. Recent breaches at major studios like Rockstar Games, Insomniac Games, and The Pokémon Company represent a new era of vulnerability, where the prize is no longer just a grainy screenshot, but the entire architectural blueprint of a multi-billion dollar franchise.
Rockstar Games found itself at the center of this storm when it refused to pay a ransom following a significant breach. While the studio managed to keep the crown jewels of the upcoming Grand Theft Auto VI relatively shielded, a trove of data regarding GTA Online was released to the public. The refusal to negotiate highlights a growing tension between corporate security protocols and the immediate damage of public disclosure. At Insomniac Games and The Pokémon Company, hackers went further still — exposing internal roadmaps, development assets, and sensitive corporate documents that stripped away the carefully curated marketing cycles both companies relied on.
From Leaks to Infrastructure Attacks
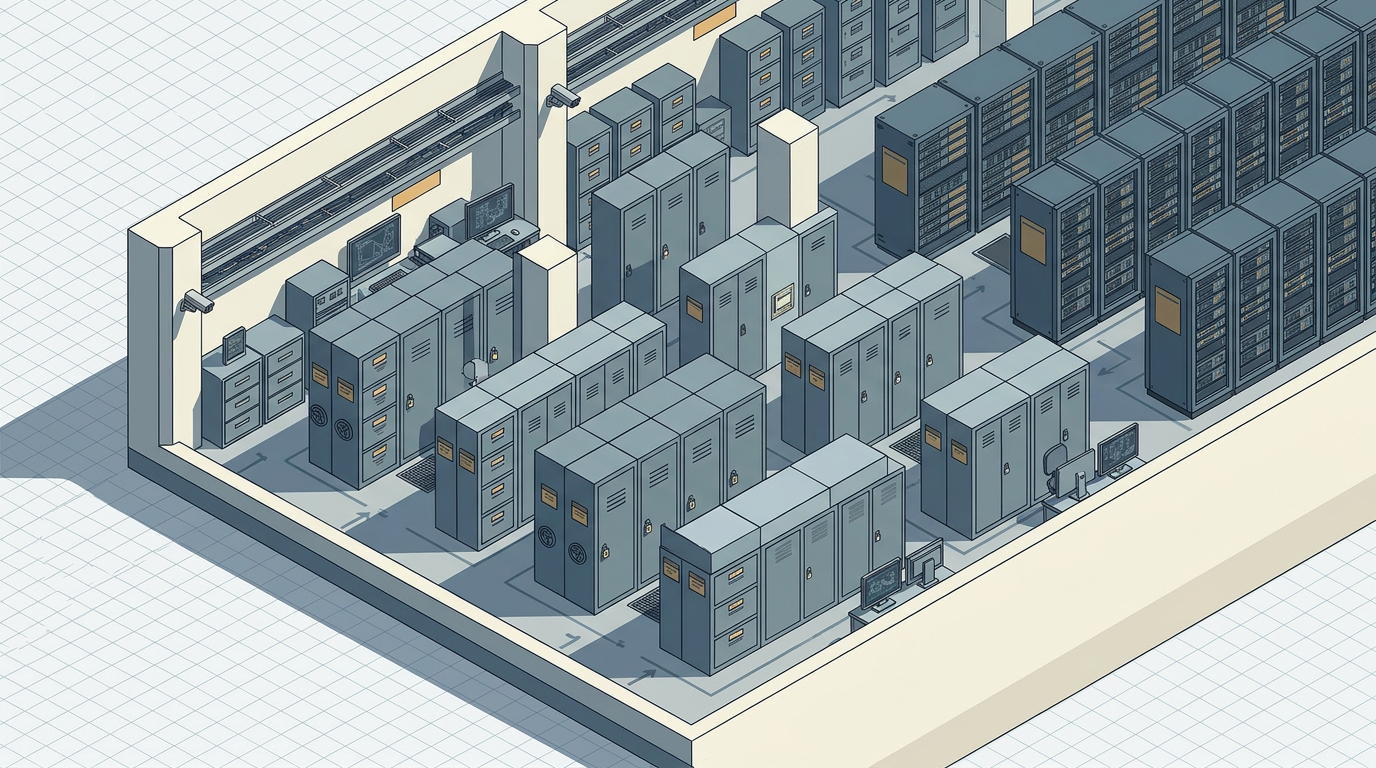
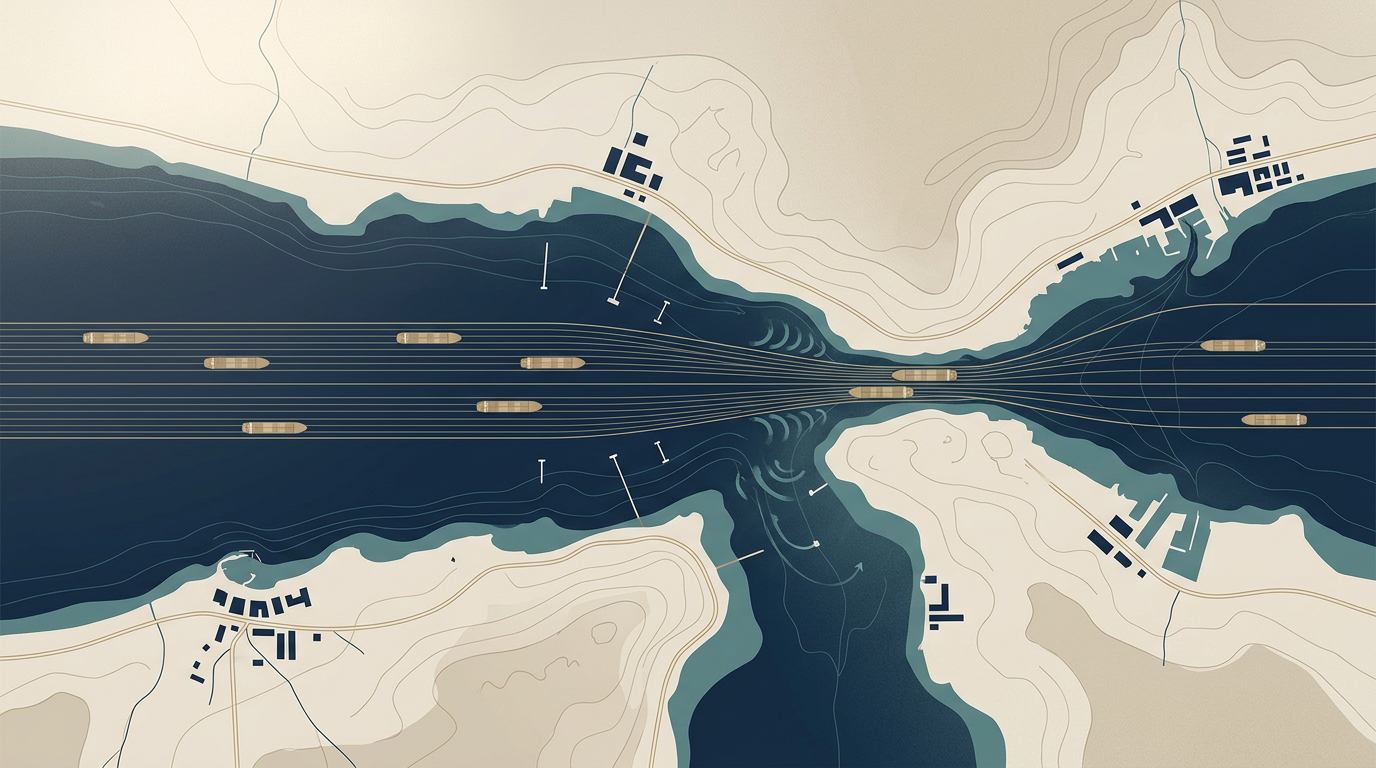
The gaming industry's security problem is not new, but its scale has changed. Early-era leaks were typically opportunistic: a prototype cartridge surfacing at a flea market, a build appearing on a file-sharing forum. The damage was reputational, rarely structural. What distinguishes the current wave is the sophistication and ambition of the attackers. Studios are no longer dealing with hobbyist hackers chasing clout. The breaches at Rockstar and Insomniac bear hallmarks of organized operations — social engineering, credential harvesting, and patient lateral movement through corporate networks — techniques more commonly associated with state-sponsored intrusions or ransomware syndicates targeting critical infrastructure.
This shift reflects a simple economic reality. A single AAA title can represent hundreds of millions of dollars in development investment and billions in projected revenue. Source code, design documents, and unreleased builds are not merely interesting — they are extraordinarily valuable, both as leverage for ransom and as intelligence for competitors or modding communities. The asymmetry is stark: studios invest heavily in the creative pipeline but historically underinvest in the security architecture that protects it. The result is a widening gap between the value of digital assets and the maturity of the defenses surrounding them.
The Cost Beyond Spoilers
Public attention tends to fixate on the consumer-facing dimension of these breaches — spoiled plot points, leaked screenshots, premature reveals. But the deeper damage is structural. When internal roadmaps surface, they expose strategic intent: planned release windows, franchise sequencing, partnership negotiations, and resource allocation decisions. This is competitive intelligence of the highest order, and once public, it cannot be retracted.
The forced transparency also disrupts the marketing machinery that modern game launches depend on. Studios orchestrate reveal cycles with the precision of a film studio or luxury brand, calibrating anticipation over months or years. A major leak collapses that timeline, compressing the window for controlled messaging and often forcing premature public statements that themselves become liabilities. Insomniac's breach, for instance, laid bare years of planned titles and internal deliberations, transforming a private development culture into an involuntary open book.
There is also a human cost that receives less attention. Leaked internal communications and personnel data can expose individual developers to harassment, doxxing, and professional harm — consequences that persist long after the news cycle moves on.
The gaming industry now sits at a crossroads familiar to other sectors that once treated cybersecurity as a secondary concern. Finance, healthcare, and energy all underwent painful reckonings before security spending matched the value of the assets at risk. Whether game publishers follow a similar trajectory — investing in zero-trust architectures, red-team exercises, and incident response capabilities commensurate with their scale — or continue to treat security as a cost center subordinate to production budgets, may determine how the next wave of breaches unfolds. The attackers, for their part, have already made their calculation.
With reporting from Canaltech.
Source · Canaltech