For years, a specific brand of digital dread has circulated among cryptographers and security professionals: the so-called "quantum apocalypse." The narrative holds that once a cryptographically relevant quantum computer (CRQC) finally arrives, the Advanced Encryption Standard with 128-bit keys — AES-128, the invisible bedrock of modern digital privacy — will essentially evaporate. The fear is largely rooted in Grover's algorithm, a quantum search procedure that theoretically halves the effective security of symmetric ciphers, reducing a 128-bit key to the equivalent of a 64-bit target. A 64-bit keyspace, in classical computing terms, is trivially breakable. The conclusion seems obvious: upgrade to AES-256 or face oblivion.
Cryptography engineer Filippo Valsorda has pushed back against this reasoning, arguing that the "halving" produced by Grover's algorithm is more mathematical abstraction than practical death sentence. The theoretical reduction in search complexity is real, but the physical constraints required to exploit it — parallelization overhead, error correction, and sheer energy consumption — tell a fundamentally different story. In the classical world, breaking AES-128 by brute force remains an absurdity; even repurposing the entirety of global Bitcoin mining hardware, the task would span billions of years. The quantum shortcut, it turns out, does not change this calculus as dramatically as popular accounts suggest.
Why Grover's Algorithm Is Not a Skeleton Key
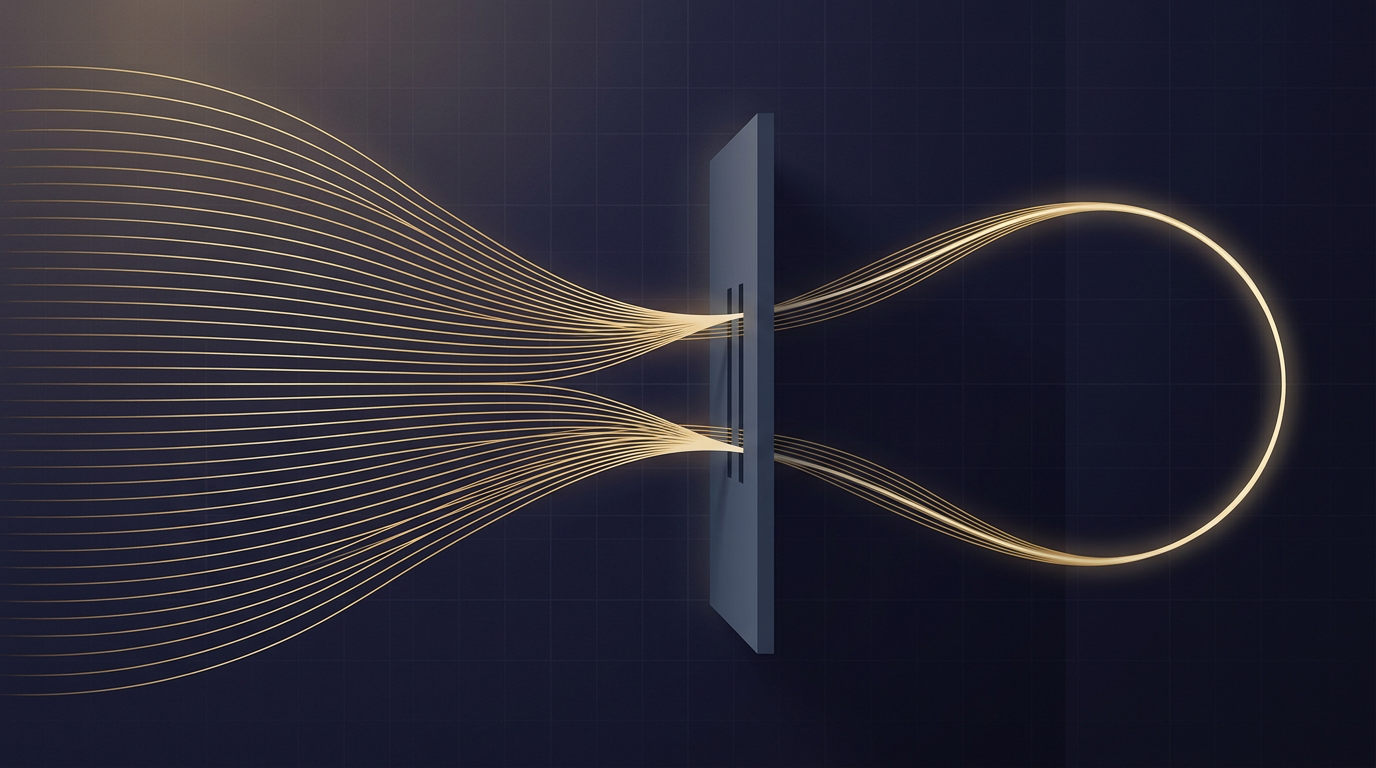
Grover's algorithm, published by Lov Grover in 1996, provides a quadratic speedup for unstructured search problems. Applied to symmetric encryption, it means that a quantum computer could, in principle, search a keyspace of 2^128 possibilities in roughly 2^64 operations. On paper, this looks devastating. In practice, the comparison obscures critical details.
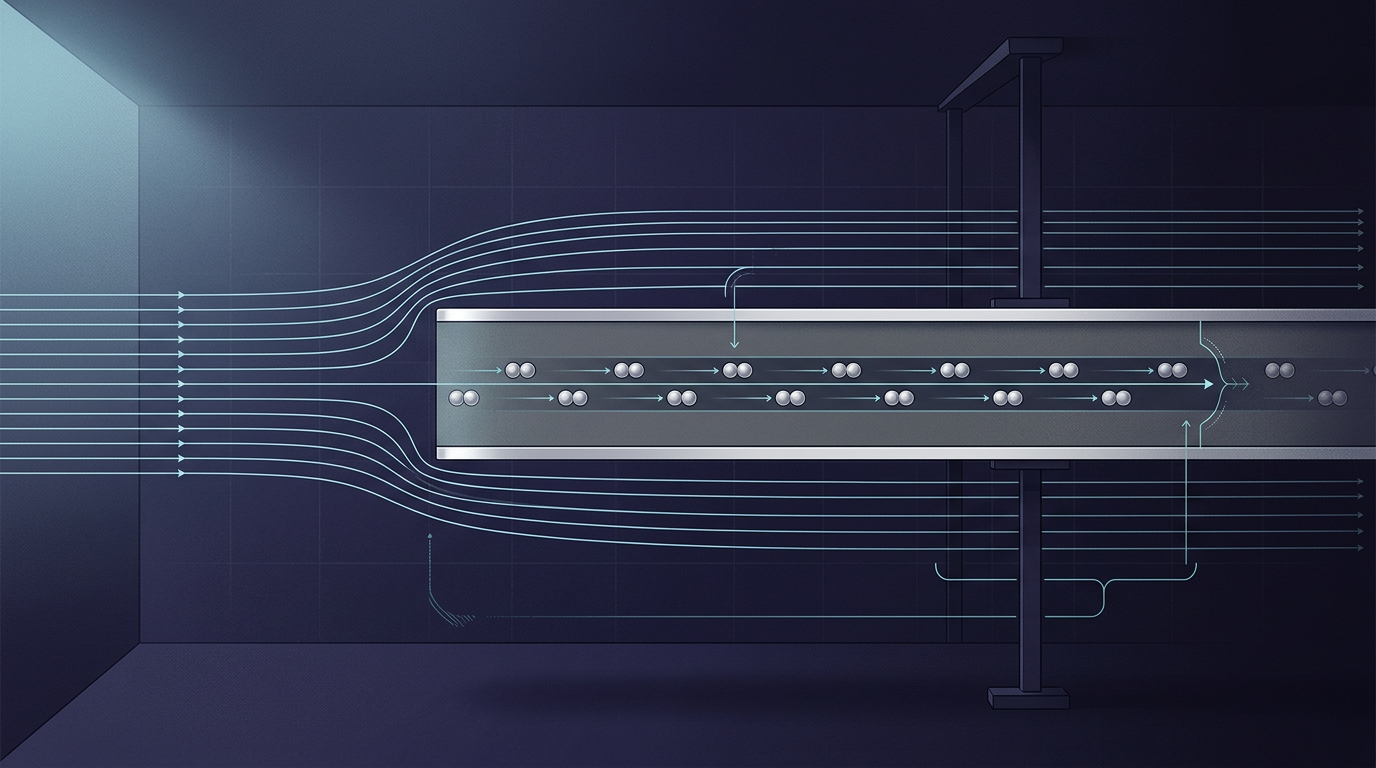
Classical brute-force attacks benefit enormously from parallelization: a problem can be split across thousands or millions of processors, each working independently. Grover's algorithm does not parallelize in the same way. Doubling the number of quantum processors does not halve the time required; the speedup is far more modest. To match the brute-force throughput that classical parallelism offers, a quantum attacker would need an extraordinary number of fault-tolerant qubits operating coherently — a hardware regime that remains far beyond current or near-term capabilities.
There is also the question of energy. Each quantum operation carries a thermodynamic cost. Estimates grounded in the Landauer limit — the minimum energy required to erase one bit of information — suggest that running Grover's algorithm against a 128-bit key at meaningful speed would require energy budgets that dwarf anything available to any entity on Earth. The theoretical halving of security bits does not account for these physical floors.
The Real Post-Quantum Battleground
None of this means the cryptographic community can afford complacency. The genuine vulnerability lies not in symmetric ciphers like AES but in public-key cryptography — the asymmetric algorithms such as RSA and elliptic-curve systems that underpin key exchange, digital signatures, and certificate infrastructure. Shor's algorithm, unlike Grover's, offers an exponential speedup against these mathematical structures, and its threat model is qualitatively different. This is why organizations like the U.S. National Institute of Standards and Technology (NIST) have spent years evaluating and standardizing post-quantum public-key algorithms, a process that has already produced new standards based on lattice and hash-based constructions.
The distinction matters for resource allocation. Migrating public-key infrastructure to post-quantum standards is an enormous engineering undertaking — touching everything from TLS handshakes to firmware signing to identity systems. If organizations simultaneously believe they must also double their symmetric key lengths, the migration grows more complex and more expensive, with marginal security benefit. AES-256 is not harmful to adopt, but treating AES-128 as broken introduces unnecessary urgency in the wrong place.
The deeper tension is between theoretical worst-case modeling and engineering pragmatism. Cryptographic standards have always been set with safety margins, and AES-128 was designed with substantial headroom against known attack classes. Grover's algorithm narrows that margin on paper without eliminating it in any physically realizable scenario. The old foundations, in this case, may prove sturdier than the ghosts haunting them — and the real work of post-quantum transition lies elsewhere, in the asymmetric algorithms where the mathematical threat is both real and imminent.
With reporting from Ars Technica.
Source · Ars Technica