The Zr.Ms. Evertsen, a Dutch Navy frigate assigned to escort the French aircraft carrier Charles de Gaulle, is among the more capable surface combatants in NATO's European fleets. Its sensor suites, missile defense systems, and electronic warfare capabilities represent decades of investment in naval survivability. Yet for several hours, the frigate's real-time position was tracked not by a peer adversary's intelligence apparatus, but by a consumer-grade Bluetooth tracker concealed inside a postcard — sent through the military's own mail service.
The breach was not the work of a hostile actor. It was a deliberate test conducted by the Dutch regional broadcaster Omroep Gelderland, which used the experiment to probe the operational security surrounding one of the Netherlands' most sensitive military assets. The journalists mailed the tracker to a crew member aboard the Evertsen, and the device — functionally similar to an Apple AirTag — began reporting its location via nearby smartphones connected to mesh-based location networks. For a period of hours, the warship's movements were visible to anyone with access to the tracker's companion app.
The Mesh Network Problem
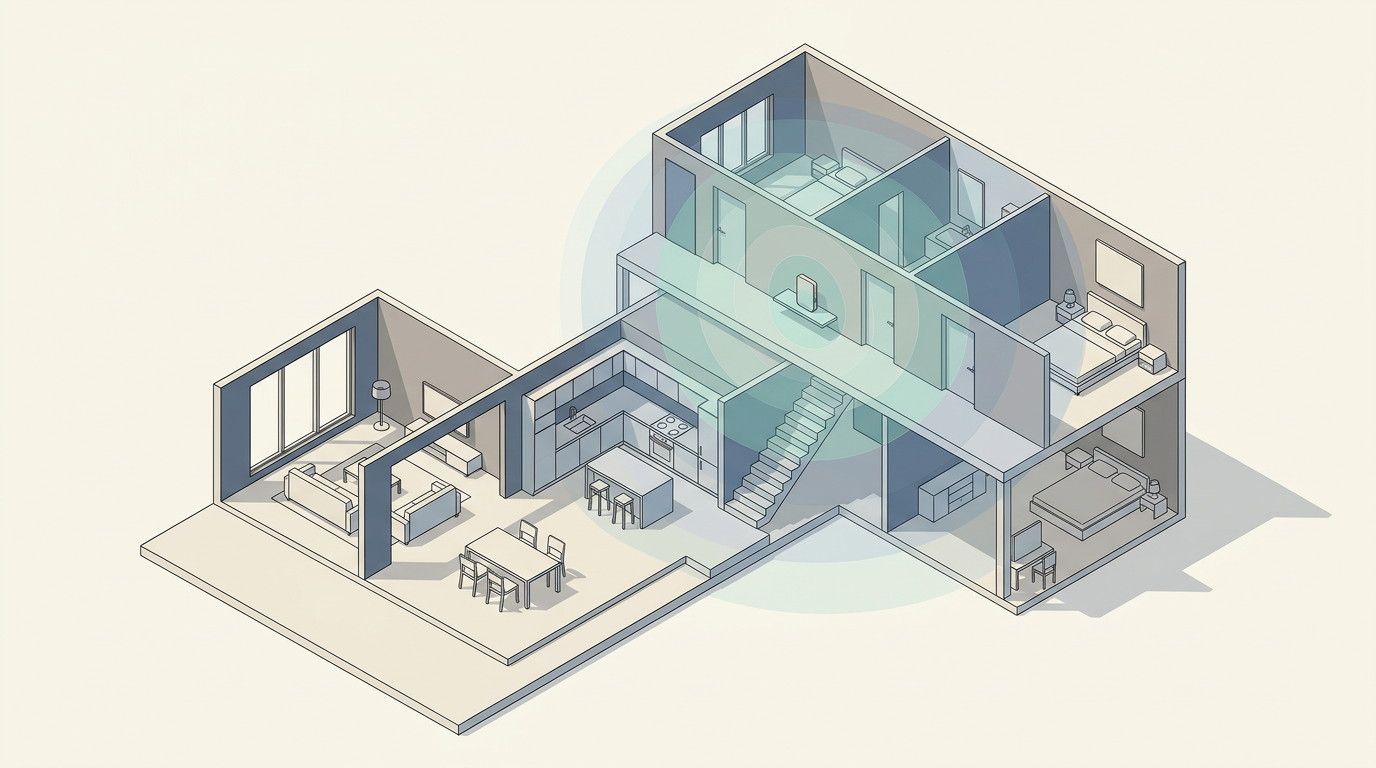
The technical principle behind the breach is straightforward. Devices like Apple's AirTag or Tile trackers do not rely on GPS or cellular connections of their own. Instead, they emit low-energy Bluetooth signals that are picked up by nearby smartphones, which then relay the tracker's location to a cloud server. The density of modern smartphone ownership means these mesh networks are effectively global. On a warship carrying hundreds of crew members — many of whom carry personal phones — the odds of at least one device detecting the tracker and forwarding its position are high.
This creates an asymmetry that traditional threat models struggle to address. Naval defense architectures are built to counter radar detection, satellite surveillance, signals intelligence, and cyber intrusion. They are not designed to neutralize a passive, commercially available device that weighs a few grams and costs less than a restaurant meal. The tracker does not emit signals that a warship's electronic warfare suite would flag as hostile. It simply exists within the ambient Bluetooth environment that modern life generates.
The Dutch Ministry of Defence has not publicly detailed what corrective measures, if any, have been implemented in response to the experiment. But the episode sits within a broader pattern. Military and intelligence agencies across NATO countries have grappled in recent years with the security implications of consumer technology aboard sensitive platforms — from fitness tracking apps that inadvertently revealed the layouts of forward operating bases to smartphones carried into classified facilities.
Logistics as Attack Surface
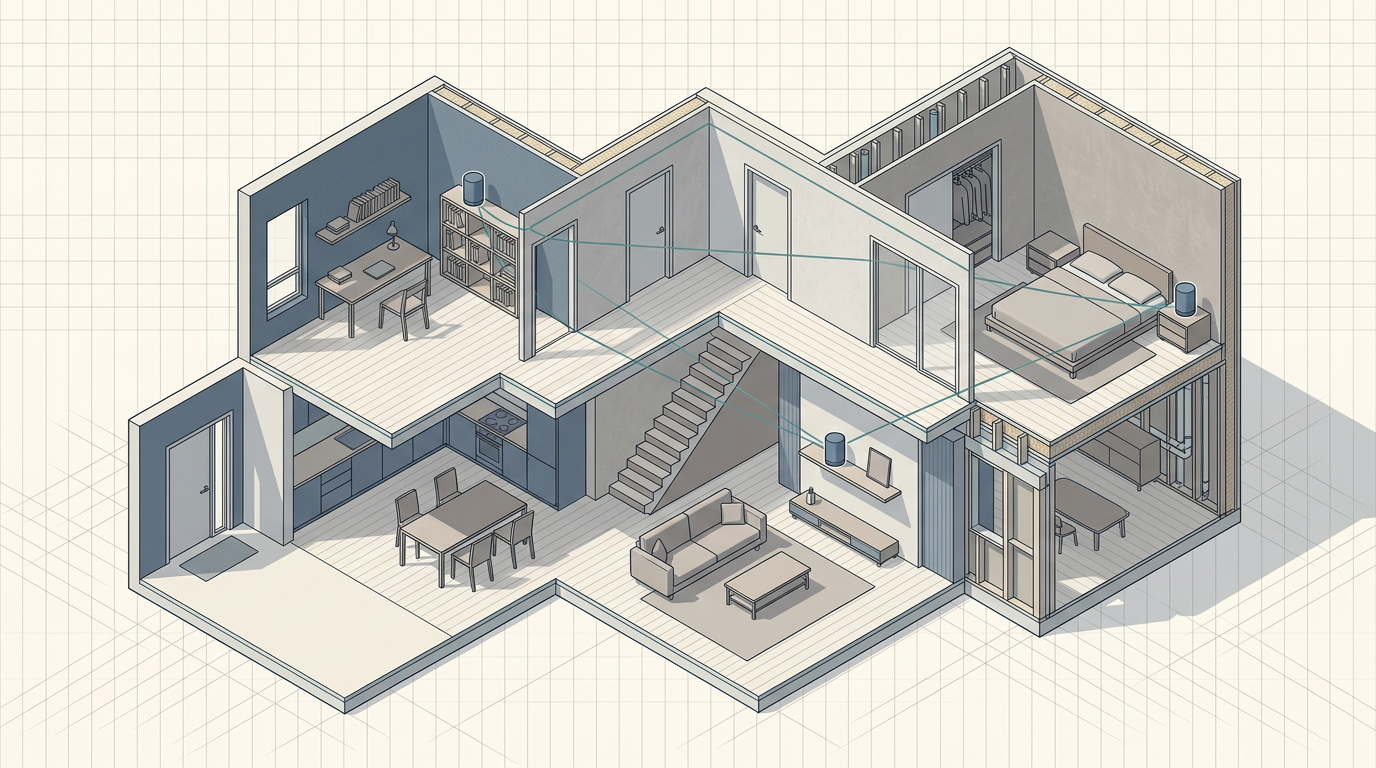
What makes the Evertsen case distinctive is the vector: military mail. Postal services to deployed personnel are a morale function with deep institutional roots. Disrupting or heavily screening mail introduces friction into a system that militaries have historically treated as low-risk. The assumption — that a postcard is benign — reflects a threat model calibrated for explosives and contraband, not for passive electronic surveillance devices smaller than a coin.
The broader implication extends beyond navies. Any organization that maintains physical perimeters while allowing routine deliveries faces a version of the same problem. Corporate campuses, diplomatic compounds, and research facilities all accept packages and mail. The proliferation of inexpensive tracking devices means that the cost of mounting a location-surveillance operation has dropped to near zero, while the cost of defending against it remains tied to labor-intensive inspection protocols.
The tension at the core of this episode is unlikely to resolve cleanly. On one side sits the operational need for security — particularly for a vessel whose mission is to protect a nuclear-powered aircraft carrier. On the other sits the reality that Bluetooth-enabled devices are now so embedded in everyday objects that screening for them would require either banning personal electronics aboard ship or deploying continuous RF-sweep capabilities tuned to consumer protocols. Each option carries its own operational and morale costs. The question is not whether militaries will adapt, but whether adaptation can keep pace with a consumer electronics ecosystem that treats ubiquitous connectivity as a feature, not a vulnerability.
With reporting from Xataka.
Source · Xataka